based on real traffic simulation and concurrent stress testing, this article conducted a systematic test on the availability, latency, anti-ddos capabilities and emergency configuration of a high-defense server deployed in a hong kong computer room in two typical business scenarios: gaming and e-commerce, and provided quantitative results and executable optimization suggestions for reference in operation, maintenance and procurement decisions.
where was the actual testing performed, and what elements did the test environment contain?
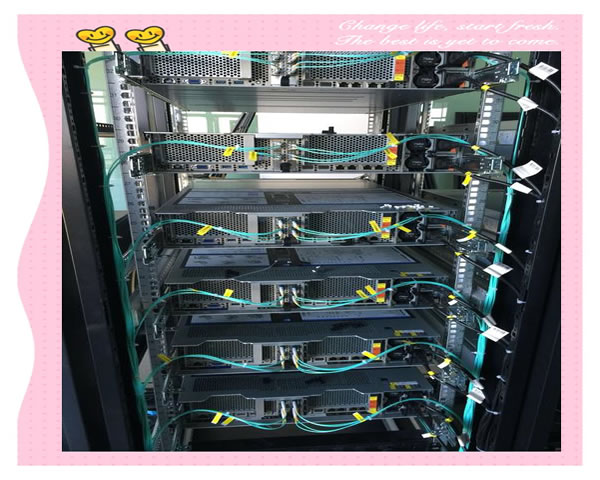
the actual test was completed in the main computer room in hong kong and its upstream backbone nodes. the test environment included: 1) real public network bandwidth access; 2) simulated player/clients distributed in multiple nodes in the asia-pacific and around the world; 3) attack simulation platform used to initiate different types of ddos (syn, udp, tcp, http-flood) and high concurrent requests; 4) business servers simulated game login/competition and e-commerce browsing/ordering processes respectively. monitoring items cover throughput, number of concurrent connections, response time and error rate.
how many protection resources are used, and how is the anti-attack capability quantified?
in the bandwidth cleaning test, when the system enabled the combination of cloud cleaning and local protection, the peak value of a single cleaning could reach more than 200gbps (the peak value of the cleaning platform). the local port and firewall rules were able to keep the business link stable when they withstood peak attacks. for l7 http flood, the request misjudgment rate is less than 2% after turning on the waf policy, and the page success rate remains above 95% under high concurrency; for udp/udp amplification attacks, the packet loss rate drops to less than 1% after cleaning takes effect, and the delay drops back to the baseline +10~30ms.
which link is most likely to become a bottleneck, and how to identify it?
testing has shown that network link bandwidth and state synchronization (such as session tables, connection tracking) are common bottlenecks. the game scene is mainly based on udp, and the server's processing power and network jitter are sensitive; the e-commerce scene is more sensitive to tls handshake and database reading and writing. identification methods include: monitoring instantaneous bandwidth, number of connections, cpu/memory and syn queue length, as well as application layer timeout and error logs, combined with traffic packet capture to confirm attack characteristics.
why does it perform better or worse in gaming scenarios, and what are the key factors?
gaming scenarios place more emphasis on low latency and no jitter than high throughput. tests show that the use of anycast+ nearby cleaning architecture and udp intelligent current limiting can significantly reduce packet loss and jitter; unreasonable strategies (such as excessive udp discarding) will directly cause players to disconnect. the key factors are the connection retention strategy, the game engine's reconnection tolerance, and the network smoothing capabilities. maintain a playable experience during attacks through qos and traffic prioritization settings.
how to protect e-commerce scenarios and which strategies are most effective?
e-commerce protection focuses on protecting critical paths (login, checkout, search). tests have shown that the combination of waf rules, behavioral analysis (rate limiting, fingerprinting), sliding verification codes and bot management can effectively intercept automated attacks without affecting real users. for high-concurrency promotion scenarios, it is recommended to use session isolation, asynchronous queues and downgrade strategies, and cooperate with cdn to cache static resources to reduce the pressure on the origin site.
how to configure it to take into account security and performance? what are the recommended necessary settings?
recommended configurations include: 1) enable cloud cleaning combined with local rate limiting; 2) deploy waf and customize core path rules (login/payment); 3) offload ssl terminals at the edge to reduce origin site cpu; 4) enable udp protection and load balancing session persistence for games; 5) configure alarms and automatic expansion policies, and perform regular stress tests and drills. the above can improve stability without significantly increasing latency.
where can monitoring and emergency procedures be further optimized to quickly restore business?
it is recommended to deploy fine-grained monitoring at the edge and origin site at the same time: the edge side monitors traffic type and cleaning trigger frequency, and the origin site monitors request distribution, error rate, and database load. establish standardized emergency scripts (such as temporarily blocking ip/asn, adjusting waf whitelist/blacklist, switching to static pages), and conduct regular drills. using siem or a unified log platform can speed up attack source tracing and false alarm troubleshooting.
which indicator best reflects the real user experience, and how to do a/b verification?
real user experience priority: page first screen time, average response delay and failure rate. you can run rum (real user monitoring) and synthetic monitoring at the same time: do baseline a/b testing during off-peak hours, and compare the above indicators and conversion rates when different protection strategies are enabled (such as strict/loose waf). find the best balance between performance and security through gradual rollback and grayscale strategies.
- Latest articles
- Can I Open A Roaming Server In Malaysia? Technical Implementation Path And Network Configuration Suggestions
- Network Design And Fault Recovery Strategy Using Malaysian Cn2 To Build A High-availability Architecture
- How Can Newbies Complete Taiwan Vps Server Rental And Resource Planning Within A Budget?
- How Overseas Users Use Japanese Native Ip L2tp To Access Local Services And Optimization Suggestions
- Stability Analysis Of Singtel's Computer Room Cn2 In Voip And Live Video Scenarios
- Best Practices For Using American Computer Room Servers In Enterprise-level Application Scenarios
- From The Perspective Of Security Operation And Maintenance, The Emergency Response And Recovery Process Of Japanese Server Cracking Software
- Technical Capabilities And Deployment Efficiency Analysis Of Common Technical Advantages Of High-quality Vietnamese Server Shops
- How To Judge Whether The Japanese Cn2 Gia Line Is Suitable For Your Website Access Needs
- Alibaba Cloud Malaysia Lightweight Server Entry-level Deployment And Performance Optimization One-step Tutorial
- Popular tags
-
The Role And Value Of Hong Kong’s Native Ip In Network Security
discuss the role and value of hong kong’s native ip in network security, and analyze its impact on information protection and network security strategies. -
Hong Kong Native Ip Airport Purchase And Usage Scenarios Detailed Explanation For Which User Groups It Is Suitable For
detailed explanation of hong kong native ip (airport) purchase and usage scenarios, including detailed steps from selecting suppliers, payment, obtaining nodes to configuration and testing on windows/macos/ios/android, as well as suggestions and faqs for which user groups it is suitable for. -
Performance Evaluation Of Hong Kong Huawei Cloud High Defense Server
in-depth analysis of the performance evaluation of huawei cloud high defense server in hong kong, answers related questions, and helps users understand its advantages and application scenarios.